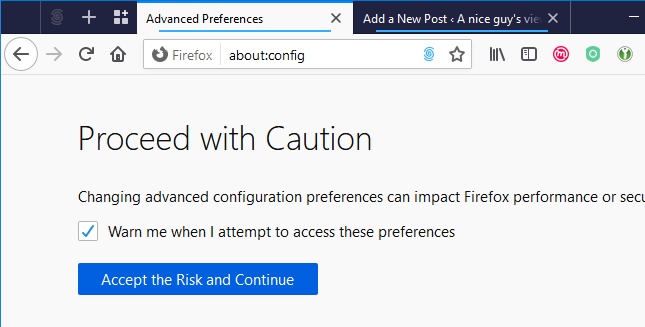
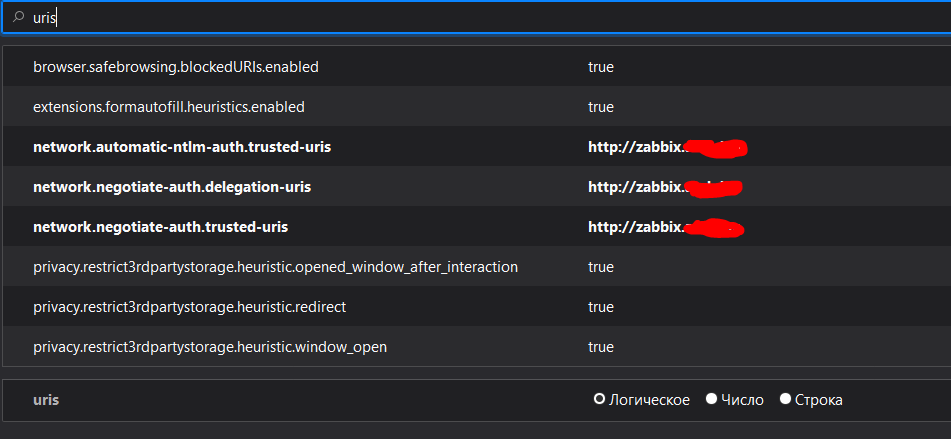
You can configure Firefox to use Kerberos for Single Sign-on. In order for this functionality to work correctly, you need to configure your web browser to send your Kerberos credentials to the appropriate KDC.The following section describes the configuration changes and other requirements to achieve this. This is because the web UI is configured for SPNEGO (Simple and Protected GSSAPI Negotiation Mechanism) to extend Kerberos to HTTP. Client must have a valid Kerberos ticket and send by browser. Mac Kerberos Client Configuration. Kerberos software is installed by default in Mac OS, but need to add configure file to access your KDC server.
Mozilla Firefox (+) Apple OS X OS X 10.9-10.11. Apple Safari (+) Google Chrome (+) Mozilla Firefox (+) Apple iOS iPhone and iPad with iOS 10. Apple Safari (+) Google Android Phones and tablets with Android 4.4 (KitKat) or later. Google Chrome (+) (+) Latest publicly released version. Browser requirements for the Report Viewer web control (2015). Note: The Extended Protection authentication setting on Windows is used to configure Kerberos mutual authentication. In this type of authentication, to prevent a man-in-the-middle attack, the server authenticates to the client and the client authenticates the server. Windows 7 on Firefox doesn't support Extended Protection. Users can enable Kerberos single sign-on (SSO) authentication using preference in their browser profile but it's also possible to set the default for all Firefox users on the system. During my ApacheCon talkthis year, one of the questions from the audience focused on.
As a student of University of California, Davis (UC Davis) you can take advantage of this service to have payments directly deposited instead of receiving a paper check.Only student financial aid refunds and student account's reimbursements can be processed through the Direct Deposit System.
To sign up for UC Davis Direct Deposit, you will need an active campus computing account (UCD Login ID and Kerberos passphrase).
Activation for Direct Deposit can take 3 - 5 business days.
Direct Deposit for employee reimbursements is now managed in UCPath. Please visit https://ucpath.ucdavis.edu/ for more information.
Supported Browsers for Direct Deposit Application:
- We recommend the latest available version (or the previous version to the latest version) of one of the following Internet browsers.
- Firefox - Firefox seems to be the best browser for the Direct Deposit application.
- JavaScript must be enabled on your browser (JavaScript is enabled by default on most browsers.)
Single sign-on (SSO) is an authentication scheme that allows a user to log in with a single ID and password to any of several related, yet independent, software systems.
True single sign-on allows the user to log in once and access services without re-entering authentication factors.
It should not be confused with same-sign on (Directory Server Authentication), often accomplished by using the Lightweight Directory Access Protocol (LDAP) and stored LDAP databases on (directory) servers.[1][2]
A simple version of single sign-on can be achieved over IP networks using cookies but only if the sites share a common DNS parent domain.[3]
For clarity, a distinction is made between Directory Server Authentication (same-sign on) and single sign-on: Directory Server Authentication refers to systems requiring authentication for each application but using the same credentials from a directory server, whereas single sign-on refers to systems where a single authentication provides access to multiple applications by passing the authentication token seamlessly to configured applications.
Conversely, single sign-off or single log-out (SLO) is the property whereby a single action of signing out terminates access to multiple software systems.
As different applications and resources support different authentication mechanisms, single sign-on must internally store the credentials used for initial authentication and translate them to the credentials required for the different mechanisms.
Other shared authentication schemes, such as OpenID and OpenID Connect, offer other services that may require users to make choices during a sign-on to a resource, but can be configured for single sign-on if those other services (such as user consent) are disabled.[4] An increasing number of federated social logons, like Facebook Connect, do require the user to enter consent choices upon first registration with a new resource, and so are not always single sign-on in the strictest sense.
Benefits[edit]
Benefits of using single sign-on include:
- Mitigate risk for access to 3rd-party sites ('federated authentication')[5] because user passwords not stored or managed externally
- Reduce password fatigue from different username and password combinations
- Reduce time spent re-entering passwords for the same identity[5]
- Reduce IT costs due to lower number of IT help desk calls about passwords[6]
SSO shares centralized authentication servers that all other applications and systems use for authentication purposes and combines this with techniques to ensure that users do not have to actively enter their credentials more than once.
Criticism[edit]
The term reduced sign-on (RSO) has been used by some to reflect the fact that single sign-on is impractical in addressing the need for different levels of secure access in the enterprise, and as such more than one authentication server may be necessary.[7]
As single sign-on provides access to many resources once the user is initially authenticated ('keys to the castle'), it increases the negative impact in case the credentials are available to other people and misused. Therefore, single sign-on requires an increased focus on the protection of the user credentials, and should ideally be combined with strong authentication methods like smart cards and one-time password tokens.[7]
Single sign-on also makes the authentication systems highly critical; a loss of their availability can result in denial of access to all systems unified under the SSO. SSO can be configured with session failover capabilities in order to maintain the system operation.[8] Nonetheless, the risk of system failure may make single sign-on undesirable for systems to which access must be guaranteed at all times, such as security or plant-floor systems.
Furthermore, the use of single-sign-on techniques utilizing social networking services such as Facebook may render third party websites unusable within libraries, schools, or workplaces that block social media sites for productivity reasons. It can also cause difficulties in countries with active censorship regimes, such as China and its 'Golden Shield Project,' where the third party website may not be actively censored, but is effectively blocked if a user's social login is blocked.[9][10]
Security[edit]
In March, 2012, a research paper[11] reported an extensive study on the security of social login mechanisms. The authors found 8 serious logic flaws in high-profile ID providers and relying party websites, such as OpenID (including Google ID and PayPal Access), Facebook, Janrain, Freelancer, FarmVille, and Sears.com. Because the researchers informed ID providers and relying party websites prior to public announcement of the discovery of the flaws, the vulnerabilities were corrected, and there have been no security breaches reported.[12]
In May 2014, a vulnerability named Covert Redirect was disclosed.[13] It was first reported 'Covert Redirect Vulnerability Related to OAuth 2.0 and OpenID' by its discoverer Wang Jing, a Mathematical PhD student from Nanyang Technological University, Singapore.[14][15][16] In fact, almost all[weasel words] Single sign-on protocols are affected. Covert Redirect takes advantage of third-party clients susceptible to an XSS or Open Redirect.[17]
In December 2020, flaws in federated authentication systems were discovered to have been utilized by attackers during the 2020 United States federal government data breach.[18][19]
Privacy[edit]
As originally implemented in Kerberos and SAML, single sign-on did not give users any choices about releasing their personal information to each new resource that the user visited. This worked well enough within a single enterprise, like MIT where Kerberos was invented, or major corporations where all of the resources were internal sites. However, as federated services like Active Directory Federation Services proliferated, the user's private information was sent out to affiliated sites not under control of the enterprise that collected the data from the user. Since privacy regulations are now tightening with legislation like the GDPR, the newer methods like OpenID Connect have started to become more attractive; for example MIT, the originator of Kerberos, now supports OpenID Connect.[20]
Email address[edit]
Single sign-on in theory can work without revealing identifying information like email address to the relying party (credential consumer), but many credential providers do not allow users to configure what information is passed on to the credential consumer. As of 2019, Google and Facebook sign-in do not require users to share email address with the credential consumer. 'Sign in with Apple' introduced in iOS 13 allows user to request a unique relay email each time the user signs up for a new service, thus reducing the likelihood of account linking by the credential consumer.[21]
Firefox Use Windows Auth
Common configurations[edit]
Kerberos-based[edit]
- Initial sign-on prompts the user for credentials, and gets a Kerberosticket-granting ticket (TGT).
- Additional software applications requiring authentication, such as email clients, wikis, and revision-control systems, use the ticket-granting ticket to acquire service tickets, proving the user's identity to the mailserver / wiki server / etc. without prompting the user to re-enter credentials.
Windows environment - Windows login fetches TGT. Active Directory-aware applications fetch service tickets, so the user is not prompted to re-authenticate.
Unix/Linux environment - Log in via Kerberos PAM modules fetches TGT. Kerberized client applications such as Evolution, Firefox, and SVN use service tickets, so the user is not prompted to re-authenticate.
Smart-card-based[edit]
Initial sign-on prompts the user for the smart card. Additional software applications also use the smart card, without prompting the user to re-enter credentials. Smart-card-based single sign-on can either use certificates or passwords stored on the smart card.
Integrated Windows Authentication[edit]
Integrated Windows Authentication is a term associated with Microsoft products and refers to the SPNEGO, Kerberos, and NTLMSSP authentication protocols with respect to SSPI functionality introduced with Microsoft Windows 2000 and included with later Windows NT-based operating systems. The term is most commonly used to refer to the automatically authenticated connections between Microsoft Internet Information Services and Internet Explorer. Cross-platform Active Directory integration vendors have extended the Integrated Windows Authentication paradigm to Unix (including Mac) and Linux systems.
Security Assertion Markup Language[edit]
Security Assertion Markup Language (SAML) is an XML-based method for exchanging user security information between an SAML identity provider and a SAML service provider. SAML 2.0 supports W3C XML encryption and service-provider–initiated web browser single sign-on exchanges. A user wielding a user agent (usually a web browser) is called the subject in SAML-based single sign-on. The user requests a web resource protected by a SAML service provider. The service provider, wishing to know the identity of the user, issues an authentication request to a SAML identity provider through the user agent. The identity provider is the one that provides the user credentials. The service provider trusts the user information from the identity provider to provide access to its services or resources.
Emerging configurations[edit]
Mobile devices as access credentials[edit]
A newer variation of single-sign-on authentication has been developed using mobile devices as access credentials. Users' mobile devices can be used to automatically log them onto multiple systems, such as building-access-control systems and computer systems, through the use of authentication methods which include OpenID Connect and SAML,[22] in conjunction with an X.509ITU-Tcryptography certificate used to identify the mobile device to an access server.
A mobile device is 'something you have', as opposed to a password which is 'something you know', or biometrics (fingerprint, retinal scan, facial recognition, etc.) which is 'something you are'. Security experts recommend using at least two out of these three factors (multi-factor authentication) for best protection.
See also[edit]
Linux Kerberos Authentication
References[edit]
- ^'What's the Difference b/w SSO (Single Sign On) & LDAP?'. JumpCloud. 2019-05-14. Retrieved 2020-10-27.
- ^'SSO and LDAP Authentication'. Authenticationworld.com. Archived from the original on 2014-05-23. Retrieved 2014-05-23.
- ^'OpenID versus Single-Sign-On Server'. alleged.org.uk. 2007-08-13. Retrieved 2014-05-23.
- ^'OpenID Connect Provider - OpenID Connect Single Sign-On (SSO) - OIDC OAuth Authentication'. OneLogin.
- ^ ab'Single sign-on and federated authentication'. kb.iu.edu.
- ^'Benefits of SSO'. University of Guelph. Retrieved 2014-05-23.
- ^ ab'Single Sign On Authentication'. Authenticationworld.com. Archived from the original on 2014-03-15. Retrieved 2013-05-28.
- ^'Sun GlassFish Enterprise Server v2.1.1 High Availability Administration Guide'. Oracle.com. Retrieved 2013-05-28.
- ^Laurenson, Lydia (3 May 2014). 'The Censorship Effect'. TechCrunch. Archived from the original on August 7, 2020. Retrieved 27 February 2015.
- ^Chester, Ken (12 August 2013). 'Censorship, external authentication, and other social media lessons from China's Great Firewall'. Tech in Asia. Archived from the original on March 26, 2014. Retrieved 9 March 2016.
- ^Rui Wang; Shuo Chen & XiaoFeng Wang. 'Signing Me onto Your Accounts through Facebook and Google: a Traffic-Guided Security Study of Commercially Deployed Single-Sign-On Web Services'.
- ^'OpenID: Vulnerability report, Data confusion' - OpenID Foundation, March 14, 2012
- ^'Facebook, Google Users Threatened by New Security Flaw'. Tom's Guide. 2 May 2014. Retrieved 11 November 2014.
- ^'Covert Redirect Vulnerability Related to OAuth 2.0 and OpenID'. Tetraph. 1 May 2014. Retrieved 10 November 2014.
- ^'Math student detects OAuth, OpenID security vulnerability'. Tech Xplore. 3 May 2014. Retrieved 10 November 2014.
- ^'Facebook, Google Users Threatened by New Security Flaw'. Yahoo. 2 May 2014. Retrieved 10 November 2014.
- ^'Covert Redirect Flaw in OAuth is Not the Next Heartbleed'. Symantec. 3 May 2014. Retrieved 10 November 2014.
- ^'VMware Flaw a Vector in SolarWinds Breach? — Krebs on Security'.
- ^Kovacs, Eduard. 'Group Behind SolarWinds Hack Bypassed MFA to Access Emails at US Think Tank'. Security Week. Security Week. Retrieved 19 December 2020.
- ^MIT IST. 'OpenID Connect Authorization'.
- ^Goode, Lauren (2019-06-15). 'App Makers Are Mixed on 'Sign In With Apple''. Wired. ISSN1059-1028. Retrieved 2019-06-15.
- ^'MicroStrategy's office of the future includes mobile identity and cybersecurity'. Washington Post. 2014-04-14. Retrieved 2014-03-30.
External links[edit]
